Something which I’ve never really talked about here is email. Me and my family currently consume Outlook.com via Windows Live Domains on both my blog domain richardjgreen.net and our personal domain name. Windows Live Domains really feels like something out of a Land Before Time movie these days. It hasn’t seen an update in years and frankly, I wonder what the shelf life of it is going forwards, leaving me to think that the options will be Outlook.com, Office 365 or bust. Not wanting to be stuck on a potentially end of the road email platform, left trying to move the mail service for my family on day zero, I started looking at options a few months back.
With Windows Live Domains being free, if I was going to pay for email, I needed it to not cost the earth, as low as possible really. At the same time, I didn’t really want anything more from a feature set than I get with Outlook.com via Windows Live Domains. All I want is a flat service to match that of Windows Live Domains and Outlook.com. With me being such a softie, the option was really only going to be Office 365, it was just a question of what tier and flavour of it.
Windows Server 2012 Essentials which I use to run our home environment has native integration for Office 365 which means it would be super easy for me to manage which for me is great as the less time I spend managing our home solution, the more time I can spend blogging, working on other things and spend more time with the family themselves.
Exchange Online vs Office 365
This really confused me when I started looking into Office 365 and using the Windows Server 2012 Essentials integration features for Office 365 sometime ago. For me and my family, I am only interested in email. I’m not after Lync or SharePoint services as we just wouldn’t use them. I was concerned that if I signed up for Exchange Online Plan 1 which was my target option that the integration wouldn’t work. As it turns out, you just need to think of everything as Office 365. Exchange Online, Exchange Online Protection, Lync Online, Enterprise Plans; all of them fall under the banner of Office 365 so I now knew that Windows Server 2012 Essentials wasn’t going to care if I was on Exchange Online Plan 1 or if I was on an Enterprise 4 agreement.
Extending the Windows Azure Tenant into Office 365
Because I use Windows Azure Backup to backup our data from Windows Server 2012 Essentials already and because this blog is hosted on Azure, I already had a tenant setup on an onmicrosoft.com domain which I wanted to reuse so I needed to extend my tenant so the one tenant would work across Windows Azure and Office 365 services. To do this, I logged into office365.com using the account which I setup as the tenant global administrator when I configured Azure Backup on Server 2012 Essentials. I was greeted with a message that I didn’t have any licenses or any domains setup, but the login worked most importantly.
Buy a Service Plan
Before you can credibly do anything, you need a plan. I wrote this post after I set it all up and lucky I did really. When I first went through the motions, I added a domain richardjgreen.net and was wondering why I couldn’t do anything with it, not even validate it. It looks like you can’t even validate a domain to start configuring users until you have at least one license available to use.
As it’s just me on my blogs domain right now, I paid up for a single license of Exchange Online Plan 1. This gives me a 50GB mailbox, all of the Exchange features I want like OWA and Exchange ActiveSync and at £2.60 a month per user excluding VAT, the price is sweet enough for me also.
To buy a license or more, all you need to od is to hit the Purchase Services link on the left navigation. This presents a whole host of options for Office 365, Exchange Online services to buy and some add-on services also such as Exchange Online Protection and Exchange Online Archiving. Add a credit card detail on file, click buy and it’s as simple as that.
Adding Custom Domains
Adding a new domain is a simple matter of clicking Domains from the left navigation and then clicking the Add a Domain button then follow the instructions which follow into setting up DNS. I had both of my domains added within a matter of a couple of mouse clicks and keystrokes.
Configuring the DNS Settings
As part of the process of adding the domain, you need to do two things:
- Verify you own the domain for starters
- Add DNS records for your services
The first step is verification which in my case, I completed by adding an MS= TXT record in my providers DNS management console. I tried to do this but I received an error “richardjgreen.net has already been verified for your account, or for another Microsoft Online Services account.”. I new I was going to see this but not quite at which stage.
This is caused by the fact that my richardjgreen.net domain was currently configured to use Windows Live Domains for email service. I logged into domains.live.com, deleted all of the mailboxes in Outlook.com for the domain and then deactivated the service. This was the most nerve racking part of the process as I’ve read that other users doing the same thing have had issues rattling on for months to get this to clear out of the system properly.
In my usual style, I kept trying the Office 365 portal to verify the domain and 15 minutes after deactivating Windows Live Domains, Office 365 pinged into life, allowing me to verify the domain.
With the first step now done, I needed to configure the service records as directed. I needed three records for my Exchange Online service: An MX record for mail delivery, a TXT record for the SPF (Sender Policy Framework, required to allow receiving servers to trust the Sender ID of outlook.com and Office 365 to deliver email on my domains behalf) and a CNAME record for Autodiscover to allow devices to be configured automatically for my mailboxes in Office 365.
If you use a DNS management agency which Microsoft have steps with then you can get direct instruction for doing this if you are little uncomfortable with DNS or if you are with GoDaddy then there is the option for an automated setup through some kind of API channel with Microsoft.
After adding the records to my DNS, it took about 10 minutes for Office 365 to pickup the new records and complete the domain setup.
Enable Office 365 Integration in Server 2012 Essentials
From my Windows Server 2012 Essentials machine, this part should have been really easy but it turned out to be a nightmare.
From the Essentials Dashboard, click Email from the home screen and then select Integrate with Microsoft Office 365. The dashboard will open a wizard for you to enter your Office 365 Tenant Global Administrator account if you already have an account as I do otherwise you have the option to initiate a free trial using an E3 subscription.
The Office 365 integration with Server 2012 Essentials is neither DirSync nor is it ADFS. If you elect to use Office 365 with Lync and SharePoint you will not get the AD FS Single Sign-On (SSO) experience as you would with a full deployment. The integration here I would describe as light. When you provision users on-premise, make changes to Office 365 licenses or mailboxes through the Dashboard, the changes are pushed up to Office 365 via a web channel which you can see from the logs (explained later).
Password synchronisation does occur so that your on-premise password and Office 365 password are in alignment however. I found this happened really quickly and my Windows Phone would report a password change required on the Office 365 email account on the phone within about a minute or so of the password change on-premise.
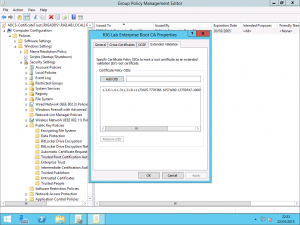
When you enable the integration, one of the things that occurs is that it forces you to enable Strong password mode on-premise which results in passwords at least eight characters in length and passwords using symbols and all the tricks in the book. Whilst I agree this is something you should be doing, if you are a small business or a home user availing of the services of Office 365 like myself, this isn’t perhaps going to be ideal. Luckily, the password policy in Office 365 is actually less strict than this. I have gone under the covers using Group Policy Management Console (GPMC) in my setup and slightly amend the Default Domain Policy GPO and all my passwords sync okay still.
The Office 365 Integration Service Gone Bad
After I ran the initial setup integration for the first time, I stopped getting any data in the dashboard. I thought it may have been a result of some pending Windows Updates so I installed those and restarted but it was still broken. I found that the problem was that the Office 365 Integration service was stopped. I started in manually and it stopped immediately with a stack trace error in the Application event log which wasn’t particularly cool.
I tried to disable the integration so that I could then re-enable it, but it appears that any operation regarding the integration requires the service to be functional. I tried to re-run the configuration but I was informed that it was already configured and I would need to disable it first which didn’t help me.
The way I got around this was to force the service to be disabled via the registry. Open Registry editor and navigate to HKLMSOFTWAREMicrosoftWindows ServerProductivity. From here, delete the key MailService and then restart the dashboard application. Doing this makes it think that the Office 365 Integration is disabled even though the dashboard will show the green tick to indicate that it’s configured. Simply re-run the configuration wizard at this point and all appears to be working now.
The Office 365 Integration Service Gone Bad Mark II
After the above happened and it all looked like it was working, I wasn’t getting password sync up to Office 365 although the Dashboard was functional to a point of allowing me to configure mailboxes. I found that the Password Sync service generates a log file in C:ProgramDataMicrosoftWindows ServerLogsSharedServiceHost-PasswordSyncProviderServerConfig.log.
Upon reading this file, I was seeing WCF errors and unhandled exceptions every few seconds which hinted to me that even though I had been able to repair the integration as far as the service health and the Dashboard were concerned, something was still amiss. I opted to this time, use the Dashboard to disable the integration, restart the server and re-configure the integration as I was now able to do this with the service for the Office 365 Integration running okay.
After removing it all and adding it again, everything worked as intended.
Configure Users
You can either do this via the Windows Server 2012 Essentials Dashboard or directly in Office 365. I’d recommend doing it in the Dashboard if you are using Essentials otherwise you have a second step to link the cloud mailbox to the on-premise user account.
To setup a user, very simply, go to the Users tab in your Dashboard. Click the user you want to activate for Office 365 and select the Assign Office 365 Account option from the tasks on the right. Pick the email address for the user using either the onmicrosoft.com or the vanity custom domain you have configured and then click Next. If you have a license available to allocate to the user, it will be setup for you. If you don’t have a free license slot then you’ll need to buy one from the site office365.com.
One thing worthy of noting is that once you enable a user for Office 365 in this way, Windows Server 2012 Essentials will set the change password on next logon flag for the user to force them into a password change with a new password for the cloud which can then by synchronised up to Office 365 for that single password login experience.
ExRCA is Your Friend
Through all of this, testing everything is working is critical. Office 365 does a good job of telling you when you’ve got things configured properly, but ExRCA or the Exchange Remote Connectivity Analyzer is better as it’s a tool dedicated for the job. Visit http://exrca.com and click the Office 365 tab and run any of the tests you like to make sure things are working. Some tests need only your domain name to verify settings such as DNS records whereas others need a credential to simulate a synthetic transaction to a mailbox or account.
I found when testing my setup that everything is reported as working but Autodiscover fails every time. When you drill into more information this is caused because the certificate name presented by the CNAME redirect from autodiscover.richardjgreen.net to autodiscover.outlook.com means that the outlook.com certificate doesn’t have my domain name on it. My Outlook and Windows Phone clients still Autodiscover the service correctly so I think this is a by-product of the Office 365 configuration and not a problem as I’ve found literally hundreds of other people asking about failed Autodiscover tests on the TechNet forums.
Client Experience
One thing I discovered which isn’t hugely clear in the documentation is that I wasn’t able to configure Outlook 2013 or my Windows Phone for ActiveSync until after I had logged in for the first time at office365.com using the account I issued my license to and configured the mailbox. You are prompted with a couple of questions such as confirming your name and time zone logging in for the first time.
After doing this online piece, Windows Phone started to sync the mailbox using ActiveSync okay, and Outlook 2013.
What’s Next
Well first I have some mail service consumers to address. I’ve got quite a few family members using Windows Live Domains with Outlook.com on our personal family domain name which I don’t fancy paying for Office 365 for so I’m going to have those tough conversations over do they want to pay for their own Office 365 mailbox or do I help them move to Outlook.com natively using a non-vanity domain. Whichever way it happens, I’m going to be looking at manual mail migrations out of Outlook.com to Office 365 for these users as there isn’t a migration path for this right now.
One thing I will be doing once I move my personal family domain over to Office 365 is implementing the Outlook Group Policy .admx files to allow Outlook to auto-configure the email address from Active Directory on first-run so that my wife and, in the future, kids don’t have to manually enter those details. It’s something I have come to expect from enterprise environments so I feel I owe them that simplicity factor enterprise computing can bring.
The kids have mail addresses right now but they aren’t live, they are aliases on our mailboxes as parents so I’m going to be looking at shared mailboxes for these to make them one step closer to full service mailboxes and I’m also going to be looking into settings up some MRM policies in Office 365 to apply to our mailboxes to keep them trim and reduce the amount of overwork we have to do to maintain the storage of it although frankly, with a 50GB mailbox, do I care?
Longer term, I may look at the option to spend an extra 65 pence a month per user and sign up to Exchange Online Protection to stem the flow of nasty emails as not everyone is as savvy as someone in IT and that’s why these services exist. It’s another one of those things for me where 65 pence per month could potentially lead to hours and entire evenings saved, not having to repair a PC after a virus got installed via an email attachment.
In more posts to come, I’ll show how I’m configuring some of the features and settings in Office 365 and I’ll talk about how I plan to upgrade my estate to Windows Server 2012 E2 Essentials to get some of the new integration and management features for Office 365 in the dashboard along with other new features.